Access control systems in 2025 are transforming security with AI, biometrics, and cloud technology. Here’s what you need to know:
- AI Integration: 91% of developers focus on AI, enabling faster responses and predictive security.
- Cloud-Based Management: 40% growth in cloud systems offers centralized control, reducing costs ($180–$250 per door annually).
- Biometric Authentication: Facial recognition, iris scanning, and palm vein tech improve security, with 23% of professionals identifying biometrics as a key trend.
- Mobile Credentials: Smartphones replace key cards, cutting costs and improving convenience with instant revocation and MFA.
- Touchless Access: Reduces lost cards (20% annually) and improves hygiene, especially in healthcare.
Cloud and AI-powered platforms simplify management, enhance security, and provide scalable, cost-effective solutions. For businesses, these systems reduce incidents and streamline operations, making them a smart upgrade from older setups.
Brief #89: Top 5 Trends in Access Control for 2025
sbb-itb-643e28e
Touchless and Keyless Access Control
The move away from physical keys and plastic cards is gaining momentum, driven by the need for better hygiene, stronger security, and easier management. Each year, about 20% of traditional key cards are either lost or stolen. Touchless and keyless systems tackle this issue by replacing cards with mobile devices and biometric authentication, setting the stage for a more secure and hassle-free access experience.
For instance, buildings using mobile credentials have seen a 40% drop in tailgating incidents. In healthcare, touchless systems have reduced surface contact by over 80%. These advancements are reshaping how security is approached, especially for property managers and business owners. For Pittsburgh businesses ready to upgrade, Sherlock’s Locksmith (https://sherlockslocksmith.com) provides installation and integration services for these modern systems. Below, we’ll explore how mobile credentials and biometric authentication are transforming access control.
Mobile Credentials
Mobile credentials essentially turn your smartphone into a digital key, using encrypted NFC and Bluetooth technology. This eliminates the need for separate fobs or plastic cards, cutting down on costs related to ordering, storing, and issuing them. Martin Huddart, Senior VP at HID, highlights the efficiency of mobile solutions:
"What mobile does is automate a lot of those physical and analog processes. We figure the payback period for upfront infrastructure work has been coming down and down as those processes become more efficient."
Another key advantage is instant revocation. If an employee leaves or a phone is lost, administrators can immediately disable access through cloud-based platforms. This reduces risks tied to lost or stolen physical items. Many systems now support Multi-Factor Authentication (MFA), combining the phone (something you have) with biometrics (something you are) to secure high-risk areas. Additionally, these digital credentials are being integrated into mobile wallets like Apple Wallet and Google Wallet, making access control feel like a regular, seamless part of daily life.
Biometric Authentication
Biometric systems use unique physical traits – like facial recognition, fingerprints, or iris scans – that are nearly impossible to fake. In fact, 32% of healthcare facilities have already adopted contactless biometrics for authentication, and 23% of industry professionals rank biometrics as one of the top three trends in access control.
When combined with mobile credentials, biometrics create a highly secure, two-layer system. Modern biometric technologies even include liveness detection to guard against fraud. This can involve passive measures, like detecting natural movements (blinking), or active prompts, such as asking users to nod or smile, to counter attempts to spoof facial recognition with photos or videos. Erin Phelps, Director of Strategic Partnerships at Aware, underscores the benefits:
"Biometric authorization integrated with mobile app platforms can strengthen the overall trend towards completely mobile-based access credentials, enabling physical access control systems of unprecedented simplicity and affordability for businesses…"
For those with privacy concerns, on-device processing is becoming more common. This approach stores and matches biometric data directly on the user’s smartphone rather than in the cloud, ensuring sensitive information stays on personal devices.
Cloud-Based Access Management
Cloud access management, built on touchless and biometric technologies, simplifies security by unifying control across multiple locations. By leveraging cloud platforms, businesses can remotely manage access without relying on on-site servers, significantly cutting down on IT expenses.
Here’s a telling statistic: cloud-based access control saw a 40% growth in 2023. This surge highlights the shift away from traditional on-premise systems, which often require manual updates and costly hardware. Kris Houle, Product Manager SaaS at Genetec, sums it up well:
"When you move into cloud technologies, you’re taking that burden off of the organization. And that, I think, is one of the major reasons why we’re seeing cloud adoption, is that high availability, the redundancy, the guaranteed uptime, the patching of cybersecurity threats."
This move toward cloud solutions enables centralized control, which is reshaping how organizations manage security.
Centralized Control Platforms
Cloud dashboards provide a streamlined way to manage hundreds of entry points through a single interface – no need for separate servers. Administrators can grant or revoke access credentials instantly, whether they’re using a laptop at the office or a smartphone during off-hours.
These platforms also integrate seamlessly with alarm systems, video surveillance, and IoT devices like CCTV and HVAC systems. For instance, if an unauthorized access attempt occurs, the system can trigger alarms, send alerts to security staff, and pull up video footage for immediate review.
Alex Kazerani, Senior Vice President at Motorola Solutions, highlights the real-world advantages:
"Cloud-based access control solutions offer real-time monitoring and data analysis to operators to help them make important decisions and enhance situational awareness."
For businesses managing multiple locations, this centralized approach is a game changer. Security teams can monitor activity, generate compliance reports, and update permissions across all sites from one dashboard – a task that would be far more cumbersome with older, on-premise systems.
But the benefits don’t stop at convenience. Cloud systems also stand out for their ability to scale and save costs.
Scalability and Cost Savings
Cloud-based solutions grow with your business. Adding new doors or locations is straightforward – just connect the necessary hardware to the cloud platform. There’s no need for additional servers or expanded local IT resources.
The pricing structure is also different. Cloud systems typically operate on a subscription model, costing around $180 to $250 per door annually. This eliminates the hefty upfront costs associated with traditional setups. As Matthew Harper, Senior Security and Risk Consultant at Jensen Hughes, explains:
"initial pricing is a difficult pitch, but long-term deployment has the potential to save clients on costs."
Savings come from multiple areas: no on-site servers, reduced IT labor, automatic security updates, and lower energy usage thanks to real-time occupancy data. Plus, modern cloud-connected control boards include onboard memory, so doors remain functional even during internet outages.
For businesses in Pittsburgh considering an upgrade from aging on-premise systems, Sherlock’s Locksmith (https://sherlockslocksmith.com) offers hardware assessments and installation services for cloud-based platforms. If your control boards are over 8–10 years old, a full migration to the cloud may be more practical than maintaining outdated equipment.
AI and Machine Learning in Access Control
Artificial intelligence is changing the game in access control, shifting from simple monitoring to actively preventing threats. Instead of just recording entries and exits, AI-driven systems analyze patterns, predict risks, and take immediate action. This advancement boosts the efficiency of keyless entry systems and cloud-based management, building on the touchless and centralized technologies already in use.
The stats are compelling: 97% of access anomalies go unnoticed in systems without AI until after an incident occurs. On the other hand, organizations using AI-based monitoring report 60% faster incident response times, turning potential breaches into non-events.
Pierre Racz, CEO at Genetec, puts it this way:
"AI stands for ‘absolute ignorance,’ and the problem with using that term is we tend to anthropomorphize it… I like IA instead – ‘intelligent automation’ – where you put a human in the loop to provide judgment and creativity and let the computer do the heavy lifting."
This blend of automation and human oversight is reshaping how businesses address security threats and verify identities.
Threat Pattern Analysis
AI systems study historical access data to define what’s considered "normal" behavior at a facility. Any deviation – like an employee trying to enter at 3 AM or a single badge being used in two locations at once – gets flagged instantly.
Machine learning also integrates with video surveillance to identify unauthorized actions, such as tailgating (when someone follows an authorized person through a secure door). These systems can trigger alarms or lockdowns without needing human intervention. AI agents, embedded in a facility’s existing camera network, can monitor for specific risks like firearms, abandoned items, or doors left ajar. Security teams even have the ability to search video footage using simple commands like "find a man in a red jacket".
The focus is now on predictive security. By analyzing patterns like repeated failed access attempts or suspicious loitering, AI systems can identify risks before they escalate. Aastha Sharma, Founder and CMO at Veris, explains:
"AI is taking access control to the next level by introducing predictive and preventive security measures… anticipating potential security breaches before they happen."
When anomalies are detected, these systems can autonomously lock down areas, alert security teams, or even adjust building conditions like lighting or HVAC to assist emergency responders. For businesses managing multiple access points, linking each entry event to corresponding video footage provides real-time verification and simplifies audits.
These predictive capabilities are further enhanced by advanced behavioral biometrics.
Behavioral Biometrics
AI has moved beyond physical identifiers like fingerprints or facial recognition to verify identity using behavioral patterns. This includes analyzing a person’s walking style (gait), typing habits (keystroke dynamics), voice, and even heartbeat using radar sensors.
This approach makes it much harder for someone to misuse stolen credentials. Even if an unauthorized person has a valid access card, they won’t get through if their behavioral data doesn’t match the registered user. Bill Moran, Vice President of Key Accounts at LenelS2, highlights this advantage:
"Advanced analytics leverage deep learning, AI, and forensics to harness vast amounts of data… These technologies help identify true security events often overlooked by human analysis, enabling organizations to proactively manage risks."
AI also adapts security requirements based on behavior and risk. For example, if someone tries to access a restricted area outside of normal hours, the system can require additional verification, like multi-factor authentication. Features like liveness detection add another layer of security, ensuring that biometric data comes from a real person – not a photo, mask, or deepfake.
For businesses in Pittsburgh looking to upgrade their security systems, Sherlock’s Locksmith (https://sherlockslocksmith.com) offers consultations on integrating behavioral biometrics. Transitioning from old Wiegand protocols to OSDP (Open Standard Device Protocol) ensures encrypted, two-way communication that supports AI-driven security needs.
Integrated Security Platforms
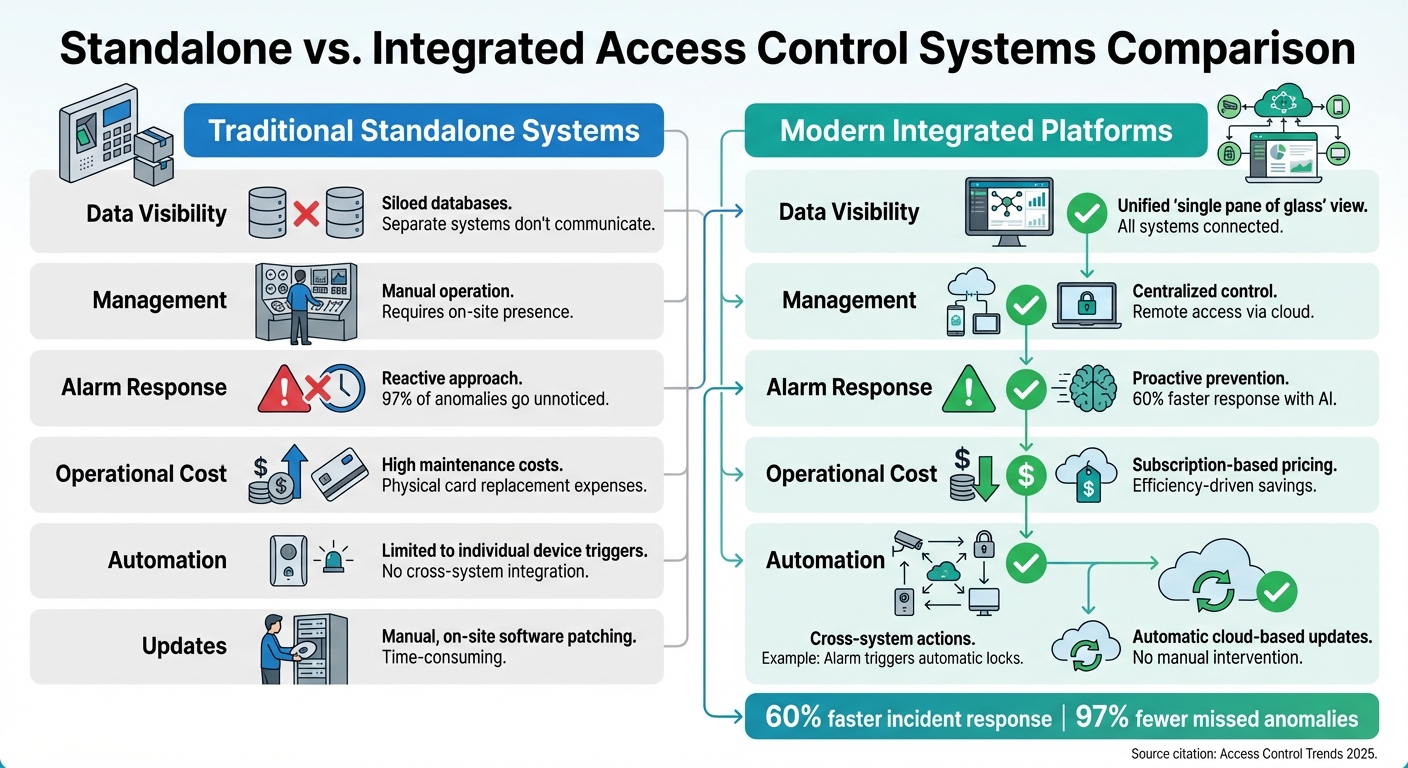
Standalone vs Integrated Access Control Systems Comparison 2025
Integrated security platforms take AI-driven and cloud-managed security to the next level by combining multiple systems into a single, streamlined interface. These platforms unify access control, video surveillance, and alarms, allowing operators to monitor and respond to incidents from one dashboard, instead of juggling multiple screens. This approach eliminates the inefficiencies and blind spots created by disconnected systems.
As Acre Security puts it:
"Security gaps thrive in silos. When your visitor management, access control, and CCTV systems don’t communicate, you lose visibility – often because systems can’t share information fast enough to prevent incidents".
The advantages of integrated systems are immediate and practical. For instance, when an alarm is triggered, the system can automatically pull up relevant video footage and access logs. Imagine a scenario where someone forces open a door: the platform can lock down other entry points, record the event, and notify security personnel within seconds. Organizations using AI-powered integrated platforms report incident response times that are 60% faster compared to traditional, standalone systems.
Katie Kistler, Director of Content at ButterflyMX, highlights this shift in expectations:
"End users are no longer satisfied with stand-alone systems that operate in silos".
Beyond security, these platforms also provide operational insights. For example, real-time occupancy data can help adjust HVAC and lighting systems to optimize energy use. Interestingly, about 40% of organizations are now using access control data for purposes beyond security, such as analytics for operational efficiency.
For businesses in Pittsburgh looking to modernize their systems, Sherlock’s Locksmith (https://sherlockslocksmith.com) offers assessments to determine if your current hardware can support integration. They note that control boards older than eight years might need replacement to meet compatibility standards.
Comparison: Standalone vs. Integrated Systems
Here’s a side-by-side look at how traditional standalone systems differ from modern integrated platforms:
| Feature | Standalone Systems | Integrated Platforms |
|---|---|---|
| Data Visibility | Siloed; separate databases for each system | Unified "single pane of glass" view |
| Management | Manual; often requires on-site presence | Centralized; remote access via cloud |
| Alarm Response | Reactive; 97% of anomalies go unnoticed | Proactive; 60% faster response with AI |
| Operational Cost | High maintenance and physical card replacement | Subscription-based; efficiency-driven |
| Automation | Limited to individual device triggers | Cross-system actions (e.g., alarm triggers locks) |
| Updates | Manual, on-site software patching | Automatic, cloud-based updates |
Geoff Kohl, Sr. Director of Marketing at SIA, captures the evolving focus of security systems:
"The value of the data from these systems became more important to the security operations than the feature set of the devices themselves".
Conclusion
Access control in 2025 is evolving far beyond traditional locks and keycards. The integration of mobile credentials, biometric authentication, cloud-based management, and AI-driven threat detection is reshaping how security is managed. These changes aren’t just theoretical; they’re already making a measurable impact. For example, 37% of end users plan to adopt AI-powered features in 2025, and over 70% of organizations using modern access control systems report fewer than five major security incidents annually.
What’s more, these systems bring financial advantages. Predictable subscription-based pricing and a reduction in physical infrastructure costs make them a smart investment. Mobile credentials, in particular, cut down on the recurring expenses tied to ordering, storing, and issuing physical badges. Together, these innovations highlight a clear trend toward better security paired with cost savings.
By combining mobile credentials, biometric technology, and cloud-based management, businesses can achieve a streamlined and secure access control solution. AI adds another layer by identifying and mitigating potential threats before they become problems. As Lee Odess, CEO of Access Control Executive Brief, puts it:
"The true winner in this digital transformation is the customer because they now choose the modality, experience, and level of assurance they desire."
For businesses and property owners in the Pittsburgh area, Sherlock’s Locksmith offers expert services to implement these advanced systems. From biometric readers to mobile-ready hardware and cloud-integrated alarm systems, their certified technicians provide installation, integration, and ongoing support to keep systems effective against evolving threats. Learn more at Sherlock’s Locksmith.
Touchless entry, smart automation, and unified security platforms are no longer optional – they’re the new standard for access control in 2025. This shift sets a higher bar for what effective security looks like in the modern era.
FAQs
How can I tell if my access control hardware supports cloud and mobile upgrades?
To figure out whether your access control hardware is ready for cloud and mobile upgrades, start by checking if it works with cloud-native or hybrid systems. These systems allow for mobile credentials and remote management, which are key for modern setups. Look over the hardware specifications for advanced features like contactless biometrics or AI capabilities. If these features aren’t present, you might need to upgrade or retrofit the hardware to keep up with current technologies.
What happens to door access if the internet goes down in a cloud-managed system?
If the internet goes down in a cloud-managed access control system, what happens next depends on how the system is built. Most systems are designed to maintain local access control, which means doors can still unlock using stored credentials. However, features like remote management, real-time monitoring, and system updates might not work until the connection is restored. To reduce the impact of outages, many systems offer hybrid or local fallback options, ensuring that essential access functions continue to operate smoothly.
How can biometrics be used without storing my biometric data in the cloud?
Biometric systems don’t always need cloud storage to function. On-device authentication methods, such as fingerprint or facial recognition, store biometric templates directly on your device. This keeps your sensitive data private and firmly under your control.
Modern mobile platforms even support multifactor authentication, blending biometrics with something like a PIN or password. This approach ensures secure access while avoiding the need to send your biometric data to external servers.









